<-References Go to ToC General Setting ->
2 Commonalities of watermarking technologies
3 General fingerprinting procedure
1 Introduction
Neural Network Traceability technologies make it possible to:
- Verify that the data provided by an Actor and received by another Actor is not compromised, i.e. it can be used for the intended scope.
- Identify the Actors providing and receiving the data.
This Chapter presents a general procedure to characterize the current practices of Neural Network Traceability technologies.
Figure 1 and Figure 2 provide general workflows for watermarking and fingerprinting, respectively.
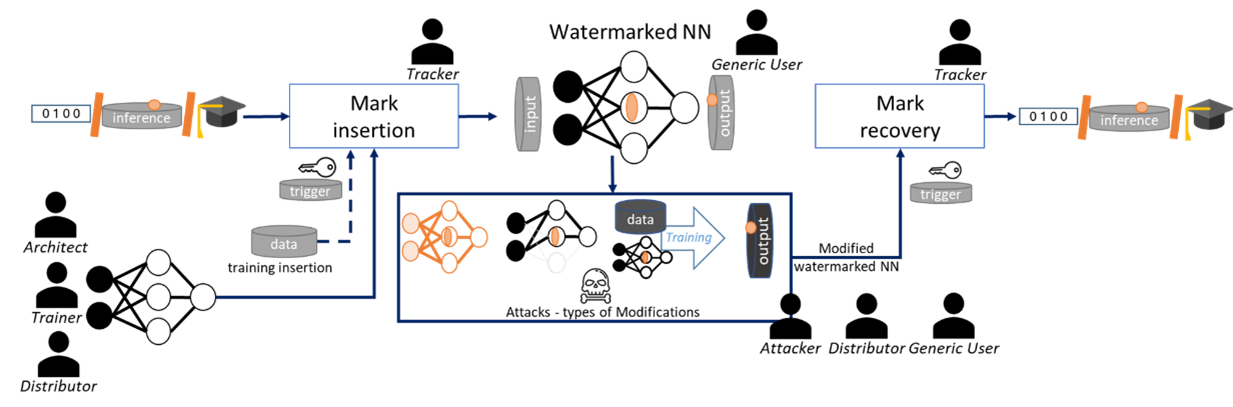
Figure 1. Synopsis of a general NN watermarking procedure
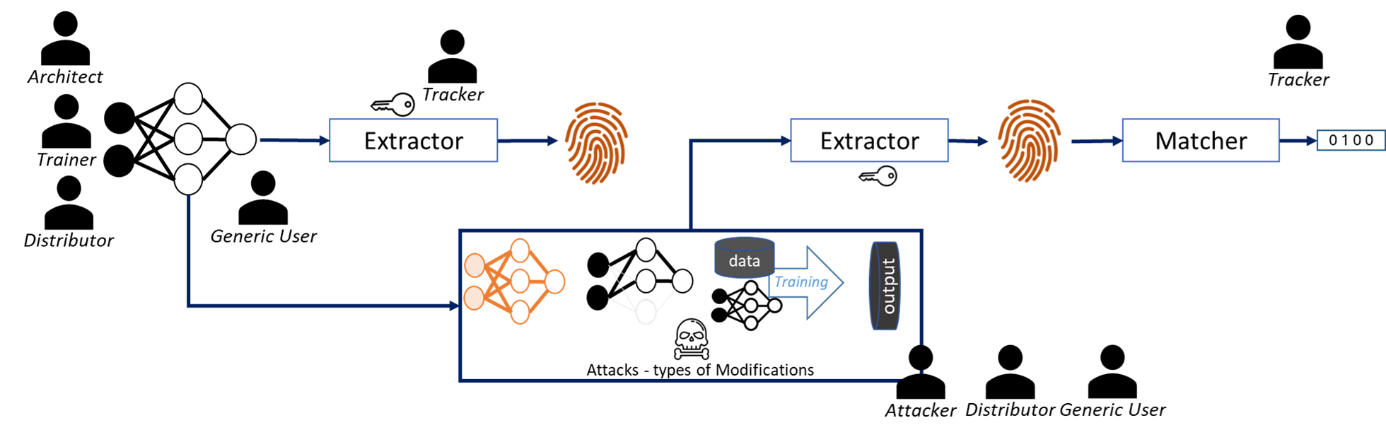
Figure 2. Synopsis of a general NN fingerprinting procedure
2 General watermarking procedure
2.1 Commonalities of watermarking technologies
Watermarking uses a family of methodological and application tools making it possible to imperceptibly and persistently insert data (also referred to as mark or watermark), that may carry a payload, into a NN [7]. Hence, watermarking is an active traceability solution, in the sense that it modifies the original content.
A watermarking method is characterized by three properties:
- Imperceptibility: the ability of a Method to not impact the performance of an NN before and after the watermark embedding insertion.
- Robustness: the ability of a Method to recover the same mark from Modified watermarked NN.
- Computational Cost: The cost of injecting, Detecting, or Decoding of a Method.
A specific application may demand different trade-offs of these 3 properties.
Watermarking solutions may use cryptography tools to ensure a high level of protection against malicious behaviours some Attacker may adopt. This standard does not consider the use of cryptographic tools.
2.2 Roles played by Actors in a watermarking lifecycle
The role of the 5 typologies of Actors is defined as follows:
- Architect: designs the architecture of the NN, cooperates in the Insertion and may also performs Modifications.
- Trainer: trains the model for a purpose, based on a dataset and Hyperparameters. When the watermarking insertion is performed during the training process, the Trainer and the Tracker may collaborate. When Modifications such as fine tuning are applied the Trainer may also collaborate.
- Tracker: provides and applies the Traceability technology to an NN and its versions resulting from applying Modifications.
- Distributor: distributes trained model with tracking technology.
- Attacker: applies Modifications to the watermarked NN. Such a role can be played either by Actors intended by the Distributor (Architect, Trainer, Tracker, Generic User) or by unintended users (generally behaving maliciously). The results of the Attacker role can be to:
- remove the Source and/or Destination IDs,
- mislead the authentication procedure,
- create ambiguity in the usage of the recovered watermark information.
Generic user: any user intended by the Distributor. They intended behaviour is regulated by the conditions they agreed to, upon subscribing to the service.
3 General fingerprinting procedure
3.1 Commonalities of fingerprinting technologies
In a neural network with passive tracing technology, some salient information (referred to as fingerprint) is extracted from the to-be-tracked NN. The Distributer and any Generic User can make decision about the identity of the tracked neural network by comparing that fingerprint to the database of fingerprints. The decision is made according to preestablished similarity measures and thresholds.
Three main properties are considered for the fingerprinting applications:
- Unicity: the ability of a method to different tracked NN result in different fingerprints
- Robustness: the ability of a method to obtain an (almost) identical fingerprint from Modified tracked NN.
- Search efficiency: the Computational Cost of extracting and matching the fingerprint.
A specific application may demand different trade-offs of these 3 properties.
Fingerprinting solutions may use cryptography tools to ensure a high level of protection against malicious behaviours some Attacker may adopt. This standard does not consider the use of cryptographic tools.
3.2 Roles played by Actors in a fingerprinting lifecycle
The role of the 5 typologies of Actors is defined as follows:
- Architect: designs the architecture of the model and is mainly involved in the Extraction step. They knowledge can also be explicitly or implicitly leveraged when Modifications are applied.
- Trainer: trains the model for a purpose, based on a dataset and on some training hyperparameters. The Trainer can also apply some Modifications.
- Tracker: provides the tracing technology.
- Distributor: distributes trained models with tracking technology.
- Attacker: applies Modifications to the NN model to be tracked.
Generic user: behaves according to the conditions agreed with the Distributor, upon subscribing to the service.

